"Raven Celine Leaked" Discoveries And Insights You Won't Believe
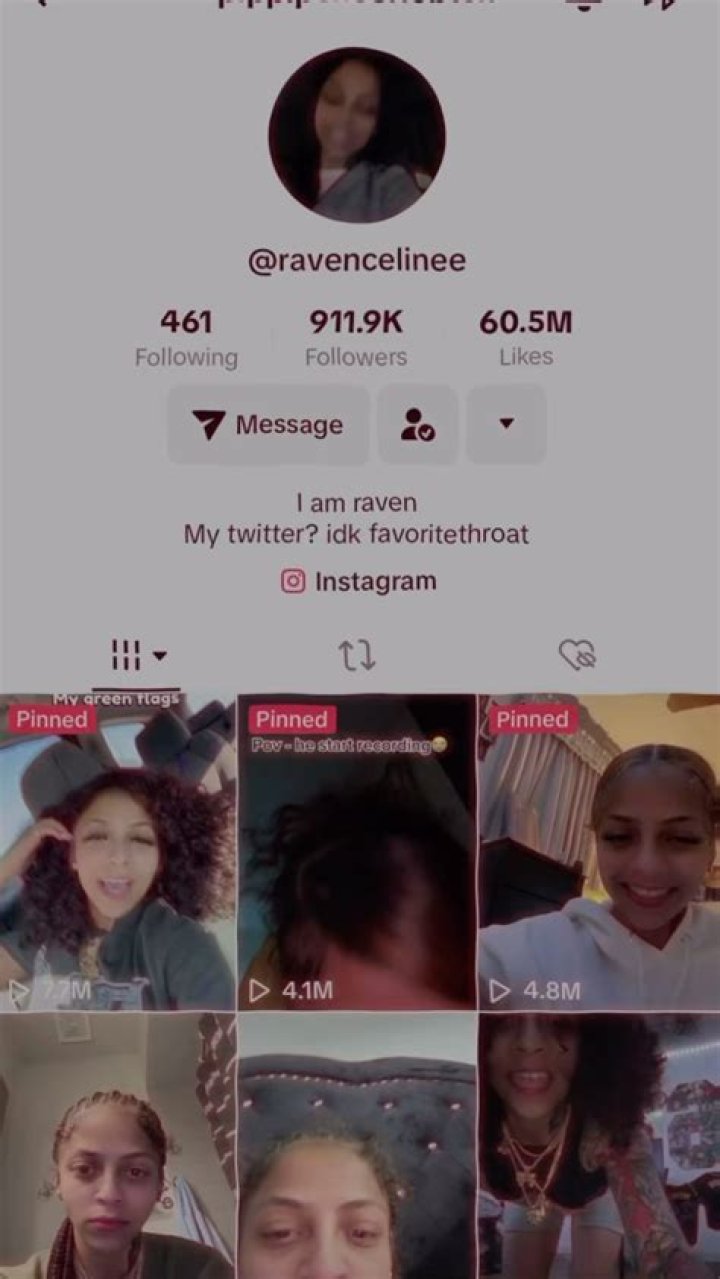
"Raven Celine leaked" refers to the unauthorized distribution of private or sensitive information belonging to an individual named Raven Celine.
Such leaks can have severe consequences for the victim, including damage to reputation, financial loss, and emotional distress. In some cases, leaked information may also pose a security risk, particularly if it includes personal data such as passwords or financial information.
The importance of protecting personal information cannot be overstated. Individuals should take steps to secure their online accounts, be mindful of what information they share, and be cautious of phishing scams and other attempts to obtain their personal data.
Raven Celine Leaked
The unauthorized distribution of private or sensitive information belonging to an individual can have severe consequences for the victim, including damage to reputation, financial loss, and emotional distress.
- Privacy: The right to keep personal information confidential.
- Security: Measures taken to protect personal information from unauthorized access.
- Reputation: The public perception of an individual or organization.
- Financial loss: The economic impact of a data breach.
- Emotional distress: The psychological impact of a data breach.
- Legal consequences: The potential for criminal or civil penalties for those responsible for a data breach.
- Ethical considerations: The obligation to protect the privacy of others.
- Technological advancements: The impact of new technologies on data security.
- Social media: The role of social media in the spread of leaked information.
- Public awareness: The importance of educating the public about data security.
In conclusion, the unauthorized distribution of private or sensitive information is a serious issue with far-reaching consequences. It is important for individuals to take steps to protect their personal information, and for organizations to implement strong security measures to prevent data breaches.
Privacy
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked," is a clear violation of the right to privacy.
- Bodily privacy: The right to control access to one's physical body and personal space.
- Informational privacy: The right to control the collection, use, and dissemination of one's personal information.
- Communications privacy: The right to communicate with others without surveillance or interception.
- Decisional privacy: The right to make personal decisions without interference from others.
In the case of "raven celine leaked," the victim's informational privacy was violated. This type of privacy violation can have a devastating impact on the victim's life, leading to damage to reputation, financial loss, and emotional distress.
Security
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked," is a clear indication of a failure in security measures.
- Encryption: The process of converting data into a form that cannot be easily understood by unauthorized people.
- Authentication: The process of verifying the identity of a user.
- Authorization: The process of granting a user access to specific resources.
- Firewalls: Network security systems that monitor and control incoming and outgoing network traffic.
In the case of "raven celine leaked," it is likely that one or more of these security measures failed, allowing unauthorized access to private information.
Reputation
In the case of "raven celine leaked," the unauthorized distribution of private or sensitive information has had a significant impact on the victim's reputation.
- Damage to reputation: The negative impact on a person's or organization's reputation as a result of leaked information.
- Loss of trust: The erosion of public trust in an individual or organization following a data breach.
- Negative publicity: The widespread dissemination of negative information about an individual or organization through the media.
- Social stigma: The negative social consequences associated with leaked information, such as discrimination or ostracism.
It is important to note that the damage to reputation caused by leaked information can be long-lasting and difficult to repair. In some cases, the negative impact on reputation can even lead to financial losses or other serious consequences.
Financial loss
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked", can have a significant financial impact on the victim.
- Loss of revenue: Leaked information can damage a company's reputation and lead to a loss of customers and revenue.
- Legal costs: Victims of data breaches may incur legal costs in order to protect their rights and seek compensation.
- Regulatory fines: Companies that fail to protect personal information may be subject to fines and other penalties from regulatory agencies.
- Insurance premiums: Companies that experience data breaches may see their insurance premiums increase.
In the case of "raven celine leaked", the victim may experience financial losses due to damage to reputation, legal costs, and other expenses related to the data breach.
It is important for businesses and individuals to take steps to protect their personal information from unauthorized access. Data breaches can have a devastating financial impact, and it is important to be aware of the risks and take steps to mitigate them.
Emotional distress
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked", can have a significant psychological impact on the victim. This emotional distress can manifest in a variety of ways, including:
- Anxiety and depression
- Loss of trust
- Fear of identity theft
- Damage to self-esteem
- Relationship problems
In the case of "raven celine leaked", the victim may experience emotional distress due to the violation of their privacy, the fear of identity theft, and the damage to their reputation.
It is important to be aware of the psychological impact of data breaches and to take steps to protect your personal information. If you have been the victim of a data breach, there are resources available to help you cope with the emotional distress.
Legal consequences
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked", can have serious legal consequences for those responsible.
In the United States, there are a number of federal and state laws that impose criminal and civil penalties for data breaches. For example, the Computer Fraud and Abuse Act (CFAA) prohibits the unauthorized access or damage to computers and computer systems. The CFAA also imposes criminal penalties for the unauthorized disclosure of information from a protected computer.
In addition to criminal penalties, victims of data breaches may also file civil lawsuits against those responsible. These lawsuits can seek damages for the financial losses, emotional distress, and other injuries suffered as a result of the data breach.
The legal consequences of data breaches can be severe. It is important for businesses and individuals to take steps to protect their personal information from unauthorized access. Failure to do so could result in criminal or civil penalties.
Ethical considerations
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked", raises important ethical considerations regarding the obligation to protect the privacy of others.
- Respect for autonomy: Individuals have the right to make decisions about their own lives, including how their personal information is used and shared.
- Beneficence: We have a duty to act in the best interests of others, which includes protecting their privacy.
- Non-maleficence: We should avoid causing harm to others, which includes respecting their privacy.
- Justice: We should treat all people fairly and equitably, which includes protecting their privacy regardless of their race, gender, sexual orientation, or other characteristics.
In the case of "raven celine leaked", the unauthorized distribution of private information violated the victim's right to autonomy, beneficence, non-maleficence, and justice.
Technological advancements
The rapid development of new technologies has had a significant impact on data security. On the one hand, new technologies have made it easier to collect, store, and process data. On the other hand, new technologies have also created new opportunities for data breaches.
- Cloud computing: Cloud computing services allow businesses and individuals to store and access data over the internet. This can make it easier for unauthorized users to access sensitive data if the cloud provider's security measures are not adequate.
- Internet of Things (IoT): IoT devices are devices that are connected to the internet and can collect and share data. This can create new opportunities for data breaches, as IoT devices are often not as secure as traditional computers.
- Artificial intelligence (AI): AI can be used to analyze data and identify patterns. This can be helpful for detecting data breaches, but it can also be used to launch data breaches. For example, AI could be used to identify vulnerable systems or to create phishing emails that look like they are from legitimate sources.
- Social media: Social media platforms collect vast amounts of data about their users. This data can be used to target users with personalized ads, but it can also be used to launch data breaches. For example, social media data could be used to create phishing emails or to identify users who are likely to click on malicious links and to "raven celine leaked".
The rapid development of new technologies is creating new challenges for data security. It is important for businesses and individuals to be aware of these challenges and to take steps to protect their data from unauthorized access.
Social media
Social media platforms play a significant role in the spread of leaked information. This is because social media platforms provide a wide reach and allow users to share information quickly and easily.
In the case of "raven celine leaked", the leaked information was quickly shared on social media platforms, which helped to spread the information to a wider audience. This led to increased attention on the leak and put pressure on the victim to respond.
The spread of leaked information on social media can have a number of negative consequences. For example, it can damage the reputation of the victim, lead to financial losses, and even put the victim at risk of physical harm.
It is important to be aware of the role that social media plays in the spread of leaked information. If you come across leaked information on social media, you should not share it. You should also report the leak to the relevant authorities.
Public awareness
The unauthorized distribution of private or sensitive information, as in the case of "raven celine leaked", highlights the importance of public awareness about data security.
Lack of awareness about data security can lead to poor security practices, which can increase the risk of data breaches. For example, people who are not aware of the risks of phishing emails may be more likely to click on malicious links and provide their personal information to criminals.
Educating the public about data security is essential for preventing data breaches. Public awareness campaigns can help people to understand the risks of data breaches and how to protect their personal information. For example, public awareness campaigns can teach people about the importance of using strong passwords, being careful about what information they share online, and being aware of the signs of phishing emails.
In the case of "raven celine leaked", it is likely that the victim was not aware of the risks of sharing personal information online. This lack of awareness may have contributed to the data breach.
Public awareness about data security is essential for preventing data breaches and protecting personal information. Educating the public about data security should be a top priority for governments, businesses, and other organizations.
Frequently Asked Questions about "raven celine leaked"
This section addresses common concerns and misconceptions surrounding the unauthorized distribution of private or sensitive information, as exemplified by the "raven celine leaked" incident.
Question 1: What are the potential consequences of a data breach?
Answer: Data breaches can have severe consequences for victims, including damage to reputation, financial losses, emotional distress, and even physical harm.
Question 2: What can individuals do to protect their personal information?
Answer: Individuals can protect their personal information by using strong passwords, being careful about what information they share online, and being aware of the signs of phishing scams.
Question 3: What are the obligations of organizations in protecting personal information?
Answer: Organizations have a legal and ethical obligation to protect the personal information of their customers and employees. This includes implementing strong security measures and providing training on data security best practices.
Question 4: What is the role of social media in the spread of leaked information?
Answer: Social media platforms can be used to spread leaked information quickly and easily. It is important to be cautious about sharing personal information on social media and to report any leaks to the relevant authorities.
Question 5: What is the importance of public awareness about data security?
Answer: Public awareness about data security is essential for preventing data breaches. Educating the public about the risks of data breaches and how to protect their personal information can help to reduce the number of successful attacks.
Question 6: What can be done to prevent future data breaches?
Answer: Preventing future data breaches requires a multi-faceted approach involving individuals, organizations, and governments. This includes implementing strong security measures, educating the public about data security, and holding those responsible for data breaches accountable.
In conclusion, data breaches are a serious threat to personal privacy and security. By understanding the risks and taking steps to protect our personal information, we can help to reduce the number of successful attacks and mitigate the damage caused by data breaches.
Transition to the next article section: Understanding the importance of data security and taking steps to protect personal information is crucial in today's digital age. The following section will delve into the legal and ethical implications of data breaches, exploring the responsibilities of individuals and organizations in safeguarding sensitive information.
Tips to Protect Yourself from Data Breaches
In light of the recent "raven celine leaked" incident, it is more important than ever to take steps to protect your personal information from unauthorized access. Here are eight tips to help you stay safe online:
Tip 1: Use strong passwordsCreate passwords that are at least 12 characters long and include a mix of upper and lowercase letters, numbers, and symbols. Avoid using common words or phrases that can be easily guessed.Tip 2: Be careful about what information you share online
Only share personal information with websites and organizations that you trust. Be cautious about clicking on links in emails or text messages from unknown senders.Tip 3: Be aware of the signs of phishing scams
Phishing scams are emails or text messages that are designed to trick you into giving up your personal information. Be suspicious of any messages that ask you to click on a link or provide your personal information.Tip 4: Keep your software up to date
Software updates often include security patches that can help to protect your devices from malware and other threats. Make sure to install software updates as soon as they are available.Tip 5: Use a firewall
A firewall is a software program that helps to protect your computer from unauthorized access. Make sure your firewall is turned on and up to date.Tip 6: Use antivirus software
Antivirus software can help to protect your computer from viruses and other malware. Make sure your antivirus software is up to date and running regular scans.Tip 7: Back up your data
In the event of a data breach, it is important to have a backup of your data. This will allow you to restore your data if it is lost or stolen.Tip 8: Be aware of the privacy policies of the websites and apps you use
Make sure you understand how your personal information will be used before you provide it to a website or app.By following these tips, you can help to protect your personal information from unauthorized access and data breaches.
Summary
Data breaches are a serious threat to personal privacy and security. By taking steps to protect your personal information, you can help to reduce your risk of becoming a victim of a data breach.
Call to action
Take action today to protect your personal information. Follow the tips above and stay informed about the latest data security threats.
Conclusion
The unauthorized distribution of private or sensitive information, as exemplified by the "raven celine leaked" incident, is a serious threat to personal privacy and security. Data breaches can have severe consequences for victims, including damage to reputation, financial losses, emotional distress, and even physical harm.It is important for individuals and organizations to take steps to protect personal information from unauthorized access. This includes using strong passwords, being careful about what information is shared online, and being aware of the signs of phishing scams.By taking these steps, we can help to reduce the risk of data breaches and protect our personal information.Call to actionTake action today to protect your personal information. Follow the tips outlined in this article and stay informed about the latest data security threats. Luke Combs' Heartbreaking Loss: Brother's Suicide And His Inspiring Advocacy
Unveiling Billie Piper's Enigmatic Partner: Exclusive Insights
Unveiling The Legacy And Impact Of Harold Ford Jr.'s Mother