Unveiling The Enigma Of Instagram Hacks: Discoveries & Solutions
Instagram account hacked refers to the unauthorized access and control of an Instagram account by an individual or group other than the account's rightful owner. This can occur through various methods, such as phishing scams, malware infections, or weak passwords, leading to the compromise of sensitive information, personal data, and account functionality.
Understanding the significance of an Instagram account being hacked extends beyond personal inconvenience. Instagram accounts have become integral to personal branding, business promotion, and social interactions. A hacked account can disrupt these activities, potentially leading to reputational damage, financial losses, and privacy concerns.
To delve deeper into the topic of Instagram account hacking, we will explore common hacking techniques, preventive measures, and recovery strategies. Additionally, we will discuss the legal implications and ethical considerations surrounding account hacking, emphasizing the importance of cybersecurity vigilance and responsible online behavior.
Instagram Account Hacking
Understanding "Instagram account hacked" encompasses various crucial aspects that delve into the nature, implications, and preventive measures surrounding this issue. Here are 10 key aspects to consider:
- Phishing Scams
- Malware Infections
- Weak Passwords
- Account Recovery
- Data Security
- Privacy Concerns
- Legal Implications
- Ethical Considerations
- Cybersecurity Vigilance
- Responsible Online Behavior
These aspects are interconnected and play a vital role in understanding the complexities of Instagram account hacking. Phishing scams, malware infections, and weak passwords are common methods used by attackers to gain unauthorized access to accounts. Understanding these techniques can help individuals strengthen their defenses and prevent account compromise. Furthermore, account recovery processes, data security measures, and privacy concerns highlight the importance of protecting personal information and maintaining control over one's online presence. Legal implications and ethical considerations emphasize the need for responsible online behavior and adherence to cybersecurity laws. By exploring these key aspects, we gain a comprehensive understanding of the issue of Instagram account hacking and the necessary steps to mitigate risks and protect our digital identities.
Phishing Scams
Phishing scams are a significant factor contributing to the prevalence of Instagram account hacking. These scams involve fraudulent emails or messages designed to trick individuals into revealing their login credentials or sensitive personal information. Scammers often create emails or messages that appear to come from legitimate sources, such as Instagram itself, and prompt users to click on a link that leads to a fake login page. Once the user enters their credentials on the fake page, the scammer gains access to their Instagram account.
Phishing scams are particularly effective because they prey on human trust and inattention. Victims may be more likely to click on a link or provide their information if they believe it is coming from a trusted source. Additionally, phishing scams are often difficult to detect, as scammers continuously adapt their techniques to bypass security measures.
Understanding the connection between phishing scams and Instagram account hacking is crucial for protecting your account and data. By being aware of the tactics used by scammers, you can be more vigilant in identifying and avoiding phishing attempts. Additionally, it is important to use strong and unique passwords for your Instagram account and to enable two-factor authentication to add an extra layer of security.
Malware Infections
Malware infections are another prevalent method used to hack Instagram accounts. Malware refers to malicious software that can infect a user's device, such as a computer or smartphone. Once installed, malware can steal sensitive information, including Instagram login credentials, and give attackers remote access to the account.
- Keyloggers: Keyloggers are a type of malware that records every keystroke made on an infected device. This allows attackers to capture Instagram login credentials and other sensitive information entered by the user.
- Trojan Horses: Trojan horses are disguised as legitimate software or apps, but once installed, they grant attackers remote access to the infected device. This can allow attackers to steal Instagram login credentials and take control of the account.
- Ransomware: Ransomware is a type of malware that encrypts files on an infected device, making them inaccessible to the user. Attackers then demand a ransom payment in exchange for decrypting the files. In some cases, attackers may also threaten to leak sensitive information, such as Instagram login credentials, if the ransom is not paid.
- Spyware: Spyware is a type of malware that monitors and collects data from an infected device, including browsing history, keystrokes, and login credentials. Attackers can use this information to hack Instagram accounts and steal sensitive information.
Understanding the connection between malware infections and Instagram account hacking is crucial for protecting your account and data. By being aware of the different types of malware and their tactics, you can take steps to prevent infections and safeguard your account. It is important to install and maintain reputable antivirus software, avoid downloading suspicious files or clicking on unknown links, and keep your operating system and software up to date.
Weak Passwords
Weak passwords play a significant role in the prevalence of Instagram account hacking. A weak password is one that is easy to guess or crack, often consisting of common words, short lengths, or a lack of special characters. Weak passwords make it easier for attackers to gain unauthorized access to Instagram accounts, as they can be brute-forced or guessed through common password dictionaries.
- Lack of Complexity: Weak passwords often lack complexity, relying on simple combinations of letters and numbers. Attackers can easily guess or brute-force these passwords, especially if they are short in length.
- Common Words: Using common words as passwords is another major weakness. Attackers can use dictionaries or rainbow tables to quickly identify and crack passwords that consist of everyday words.
- Personal Information: Incorporating personal information, such as names, birthdates, or pet names, into passwords weakens their security. Attackers can often gather this information from social media profiles or other online sources.
- Reused Passwords: Reusing the same password across multiple accounts increases the risk of compromise. If one account is hacked, attackers can potentially gain access to all accounts using the same password.
Understanding the connection between weak passwords and Instagram account hacking is crucial for protecting your account and data. By creating strong and unique passwords, you can significantly reduce the risk of unauthorized access. Strong passwords should be at least 12 characters long, contain a mix of uppercase and lowercase letters, numbers, and special characters, and avoid common words or personal information.
Account Recovery
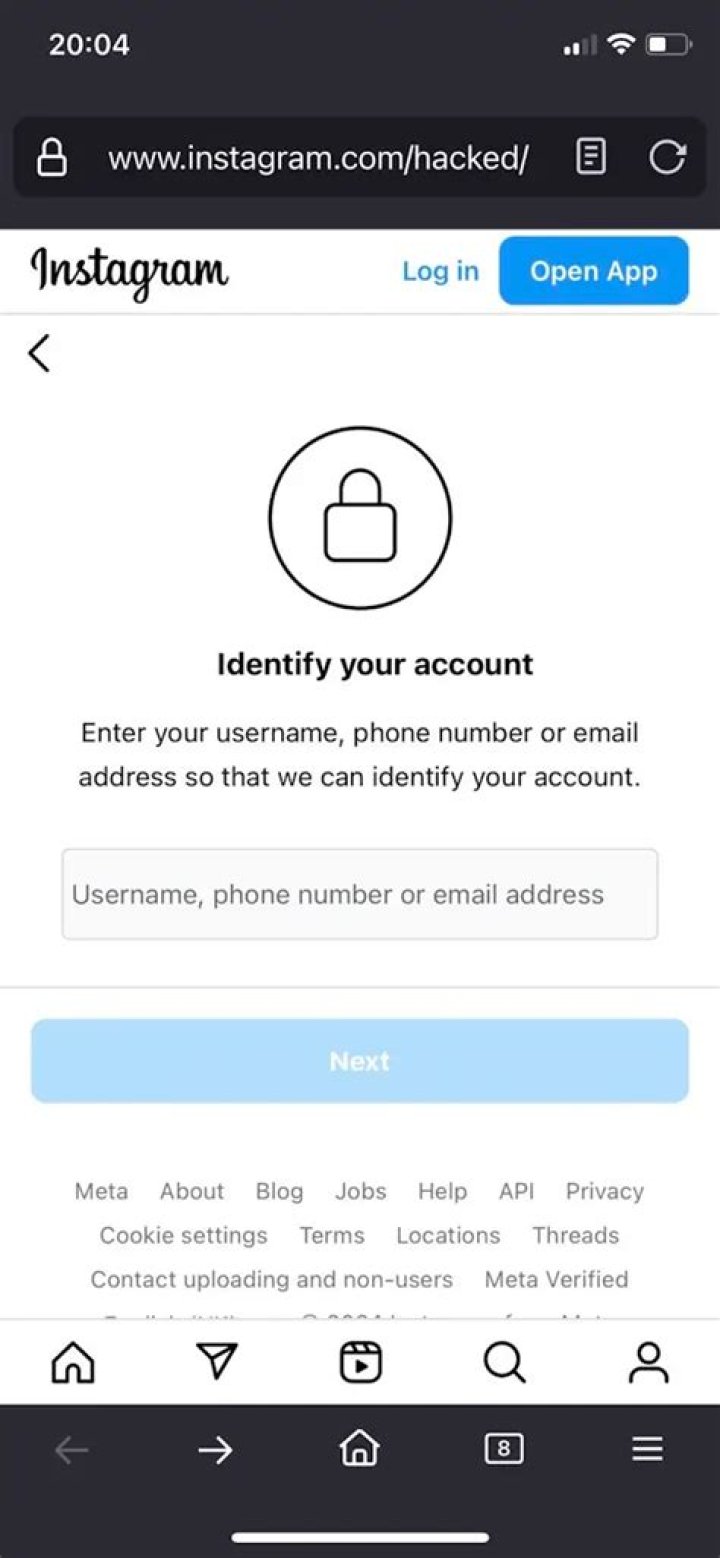
Account recovery plays a critical role in the context of "Instagram account hacked." When an Instagram account is hacked, the account holder may lose access to their profile, personal information, and content. Account recovery provides a mechanism for users to regain control of their compromised accounts and minimize the impact of the hack.
The account recovery process involves verifying the user's identity through various methods, such as email, phone number, or linked social media accounts. Once the user's identity is verified, they can reset their password and regain access to their account. This process helps prevent unauthorized individuals from maintaining control of the hacked account.
Understanding the connection between account recovery and Instagram account hacking is crucial for users to take proactive steps to protect their accounts. By enabling two-factor authentication, using strong passwords, and being cautious of suspicious emails or messages, users can reduce the risk of their accounts being hacked. In the event of a hack, knowing the account recovery process and acting promptly can help users regain control of their accounts and minimize the potential damage.
Data Security
Data security plays a crucial role in the context of "Instagram account hacked." When an Instagram account is hacked, the attacker gains access to the user's personal information, including their profile data, messages, photos, and videos. This information can be used for identity theft, financial fraud, or other malicious purposes.
There are several ways in which data security is compromised in the context of Instagram account hacking. One common method is through phishing scams, where attackers send emails or messages that appear to come from Instagram and trick users into revealing their login credentials. Another method is through malware, which can be installed on a user's device and steal their Instagram login information.
Understanding the connection between data security and Instagram account hacking is critical for users to take proactive steps to protect their accounts. By using strong passwords, enabling two-factor authentication, and being cautious of suspicious emails or messages, users can reduce the risk of their accounts being hacked and their personal information being compromised.
Privacy Concerns
The connection between "Privacy Concerns" and "Instagram account hacked" is significant, as a hacked Instagram account can lead to the exposure and misuse of personal and sensitive information.
- Identity Theft
Hackers can use the personal information obtained from a hacked Instagram account, such as, email address, and date of birth, to steal the victim's identity. This can lead to financial fraud, such as unauthorized access to bank accounts or credit cards, and other serious consequences.
- Financial Fraud
Hackers can also use the financial information linked to a hacked Instagram account, such as credit card numbers or PayPal accounts, to make fraudulent purchases or withdraw funds. This can result in financial losses and damage to the victim's credit score.
- Reputation Damage
Hackers can post damaging or embarrassing content on a hacked Instagram account, or send messages to the victim's followers, damaging their reputation and relationships.
- Cyberbullying and Harassment
Hackers can use a hacked Instagram account to cyberbully or harass the victim, sending abusive or threatening messages, or posting personal information without their consent. This can have severe emotional and psychological consequences.
These concerns highlight the importance of protecting Instagram accounts from hacking and the potential risks associated with compromised privacy. By understanding the connection between "Privacy Concerns" and "Instagram account hacked," individuals can take steps to safeguard their personal information and maintain control over their online presence.
Legal Implications
The connection between "Legal Implications" and "Instagram account hacked" is significant, as unauthorized access to and control of an Instagram account can lead to various legal issues and consequences.
One of the primary legal implications is the violation of the Computer Fraud and Abuse Act (CFAA). The CFAA prohibits unauthorized access to computer systems and data, including social media accounts like Instagram. Individuals who hack into Instagram accounts can be subject to criminal charges and penalties under the CFAA.
Furthermore, hacking into an Instagram account may constitute a violation of state laws against computer crimes and identity theft. In many jurisdictions, it is illegal to obtain or use another person's personal information without their consent, and hacking into an Instagram account can be considered a form of identity theft.
Additionally, the misuse of hacked Instagram accounts can lead to civil lawsuits. For example, if a hacker posts defamatory or harassing content on a hacked account, the victim may have grounds to file a lawsuit for damages.
Understanding the legal implications of Instagram account hacking is crucial for individuals and businesses alike. Taking steps to protect Instagram accounts from hacking, such as using strong passwords and enabling two-factor authentication, can help mitigate the risk of legal consequences.
Ethical Considerations
The connection between "Ethical Considerations" and "Instagram account hacked" is significant, as hacking into an Instagram account raises several ethical concerns and dilemmas.
- Privacy Violation
Hacking into an Instagram account is a clear violation of the account holder's privacy. It involves accessing and potentially misusing their personal information, messages, photos, and other content without their consent. This can have severe consequences for the victim, including identity theft, financial fraud, and reputational damage.
- Unauthorized Access
Hacking into an Instagram account is an unauthorized access to a private online space. It violates the user's right to control and manage their own account and content. Hackers may use the account to spread misinformation, harass others, or engage in other malicious activities, damaging the victim's reputation and well-being.
- Cyberbullying and Harassment
Hacked Instagram accounts can be used as a platform for cyberbullying and harassment. Hackers may post defamatory or threatening content, impersonate the victim to send abusive messages, or share private information without consent. This can have severe emotional and psychological consequences for the victim, including anxiety, depression, and even suicidal thoughts.
- Property Rights
Instagram accounts and the content within them are considered personal property. Hacking into an account and stealing or misusing content violates the victim's property rights. Hackers may use stolen content for commercial gain, distribute it without permission, or alter it to damage the victim's reputation.
These ethical considerations highlight the importance of respecting the privacy, autonomy, and property rights of others online. Hacking into Instagram accounts is not only illegal but also a serious ethical violation that can have far-reaching consequences for the victims.
Cybersecurity Vigilance
The connection between "Cybersecurity Vigilance" and "Instagram account hacked" is crucial, as proactive measures to safeguard online accounts can significantly reduce the risk of unauthorized access and compromise. Cybersecurity vigilance involves the implementation of best practices and security measures to protect against potential threats and vulnerabilities.
- Strong Passwords
Using strong and unique passwords is essential to prevent unauthorized access to Instagram accounts. Avoid using common words, personal information, or easily guessable combinations. Regularly updating passwords and enabling two-factor authentication adds an extra layer of security.
- Suspicious Email and Message Detection
Phishing scams and malicious links are common methods used to trick users into revealing their login credentials. Be cautious of emails or messages from unknown senders or those that appear suspicious. Never click on links or provide personal information unless you are certain of the sender's authenticity.
- Software Updates and Security Patches
Keeping software and operating systems up to date is crucial to address security vulnerabilities that could be exploited by attackers. Regularly installing software updates and security patches helps protect against known threats and reduces the risk of malware infections.
- Account Monitoring and Activity Tracking
Regularly monitoring account activity and tracking logins from unrecognized devices can help identify suspicious activity. Instagram provides features to review login history and receive notifications for unusual login attempts, allowing users to take prompt action if needed.
By practicing cybersecurity vigilance and implementing these measures, Instagram users can significantly reduce the risk of their accounts being hacked. It is important to remain vigilant and aware of potential threats to protect personal information, privacy, and the integrity of online accounts.
Responsible Online Behavior
Responsible online behavior plays a crucial role in preventing Instagram account hacking. By understanding the connection between the two, individuals can take proactive steps to safeguard their accounts and protect their personal information.
One key aspect of responsible online behavior is avoiding suspicious links and attachments. Phishing scams are a common method used by hackers to gain access to Instagram accounts. These scams often involve emails or messages that appear legitimate but contain malicious links or attachments. By being cautious and avoiding clicking on suspicious links, users can significantly reduce the risk of their accounts being compromised.
Additionally, using strong and unique passwords is essential for responsible online behavior. Weak or easily guessable passwords make it easier for hackers to gain unauthorized access to accounts. Creating strong passwords that are unique to each account helps protect against brute-force attacks and other hacking attempts.
Furthermore, enabling two-factor authentication adds an extra layer of security to Instagram accounts. When two-factor authentication is enabled, users are required to provide a second form of authentication, such as a code sent to their phone, when logging into their accounts. This makes it much more difficult for hackers to gain access, even if they have obtained the user's password.
In conclusion, responsible online behavior is essential for preventing Instagram account hacking. By avoiding suspicious links, using strong passwords, and enabling two-factor authentication, users can significantly reduce the risk of their accounts being compromised and protect their personal information.
Frequently Asked Questions about Instagram Account Hacking
Understanding the common concerns and misconceptions surrounding Instagram account hacking is essential for protecting your account and personal information. Here are answers to six frequently asked questions:
Question 1: What are the most common ways Instagram accounts get hacked?
Hackers commonly employ phishing scams, malware infections, and weak passwords to gain unauthorized access to Instagram accounts.
Question 2: How can I prevent my Instagram account from being hacked?
To protect your account, use strong and unique passwords, enable two-factor authentication, be cautious of suspicious links and attachments, and keep your software up to date.
Question 3: What should I do if my Instagram account is hacked?
If your account is compromised, act promptly by changing your password, reporting the hack to Instagram, and enabling two-factor authentication.
Question 4: Can I recover my hacked Instagram account?
Account recovery is possible if you have access to the email address or phone number associated with your account. Follow the steps provided by Instagram to regain control.
Question 5: What are the consequences of an Instagram account hack?
Hacked accounts can lead to identity theft, financial fraud, privacy violations, and reputational damage.
Question 6: Is it possible to track down and punish the person who hacked my Instagram account?
Tracking down and punishing the hacker can be challenging, but reporting the incident to law enforcement or cybersecurity authorities may help initiate an investigation.
Remember, staying vigilant and practicing responsible online behavior are crucial for safeguarding your Instagram account and personal information.
Transition to the Next Section: Understanding the Importance of Cybersecurity
Tips to Protect Your Instagram Account from Hacking
Understanding the severe consequences of an Instagram account hack, such as identity theft and privacy violations, demands proactive measures to safeguard your account. Implementing these effective tips can significantly minimize the risk of unauthorized access and protect your personal information.
Tip 1: Create Strong and Unique Passwords
Avoid using weak or easily guessable passwords. Instead, opt for strong passwords that are at least 12 characters long and include a combination of uppercase and lowercase letters, numbers, and special characters. Make sure each password is unique to your Instagram account and not used for any other online service.
Tip 2: Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security to your account by requiring you to provide a second form of verification, such as a code sent to your phone, when logging in. This makes it much more difficult for hackers to gain access to your account, even if they have your password.
Tip 3: Be Cautious of Suspicious Links and Attachments
Phishing scams are a common method used by hackers to trick users into revealing their login credentials. Avoid clicking on suspicious links or opening attachments in emails or messages from unknown senders. If you're unsure whether a link is legitimate, hover over it to see the actual destination URL.
Tip 4: Keep Software Up to Date
Regularly updating your operating system, browser, and Instagram app helps protect against vulnerabilities that hackers can exploit. Software updates often include security patches that fix known weaknesses and make it harder for hackers to gain access to your devices and accounts.
Tip 5: Report Suspicious Activity
If you notice any unusual activity on your Instagram account, such as unauthorized login attempts or changes to your profile information, report it to Instagram immediately. You can do this through the app's settings or by contacting Instagram's support team.
Summary of Key Takeaways
By implementing these tips, you can significantly reduce the risk of your Instagram account being hacked. Remember to stay vigilant, protect your personal information, and report any suspicious activity promptly. Safeguarding your online presence is crucial in today's digital world, and these measures will empower you to maintain control over your Instagram account and protect your privacy.
Transition to the Article's Conclusion
Understanding the serious consequences of an Instagram account hack and implementing these proactive tips will help you safeguard your account, protect your privacy, and maintain control over your online presence.
Conclusion
Understanding the concept of "Instagram account hacked" is crucial in today's digital landscape. This article explored the various methods used by attackers to gain unauthorized access to Instagram accounts, emphasizing the importance of cybersecurity vigilance and responsible online behavior. By implementing strong passwords, enabling two-factor authentication, and being cautious of suspicious links and attachments, individuals can significantly reduce the risk of their accounts being compromised.
The consequences of an Instagram account hack can be severe, ranging from identity theft and financial fraud to privacy violations and reputational damage. Therefore, it is imperative to take proactive measures to protect your account and personal information. Stay informed about the latest hacking techniques, report suspicious activity promptly, and spread awareness about the importance of cybersecurity. By working together, we can create a safer and more secure online environment for everyone.